How to Setup Exchange Server 2007
Follow the steps below to correctly configure your Exchange Server 2007 email server for general use, and for use with IGetMail. Note that for this document we are assuming you are installing Exchange 2007 on Windows Server 2008 64-Bit.- Pre-Installation Checklist
- Install Windows Server 2008 64-bit version
- Configure your static IP address
- Activate Auto Updates
- Add role - Active Directory Services
- Add role - Active Directory Lightweight Services
- Add feature - Windows Process Activation Service
- Add role - Web Server (IIS)
- Add feature - PowerShell
- Roles / Features NOT to install
-
- Installing Exchange Server 2007
- Allow Mail access to your Exchange Server
- Adding E-Mail Users
Make sure you have all of the following steps in place before you setup Exchange Server 2007 on Windows Server 2008 64-Bit.
For simplicity we are assuming you are setting up a small office where one machine will be used for both the Active Directory and the Exchange Server. This setup works just fine and reduces the number of machines to maintain. If you have a larger office you may want to consider separating the Active Directory machine and the Exchange 2007 Server.
Install Windows Server 2008 64-bit version
Exchange 2007 is a 64-bit application and requires 64-bit versions of Windows Server 2003 or Windows Server 2008. You should select a computer that is capable of running the 64-bit version of Windows Server 2003 or 2008. For this example we will start with a clean installation of Windows Server 2008 64-bit version that has not had any roles installed.
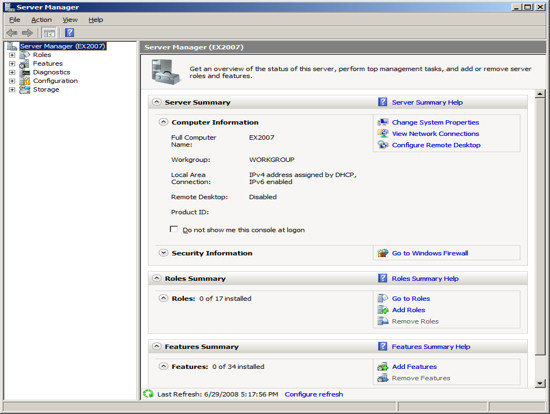
After installing Windows Server 2008, we set the clock and the name of the server to be "EX2007". At this point this server is configured to be a stand-alone computer with default settings.
Configure Your Static IP Address
The default installation of Windows 2008 sets your IP v4 and IP v6 addresses to use DHCP. Since we will be configuring this computer to be a domain controller, you must change the IP address of the computer to be a static IP address.
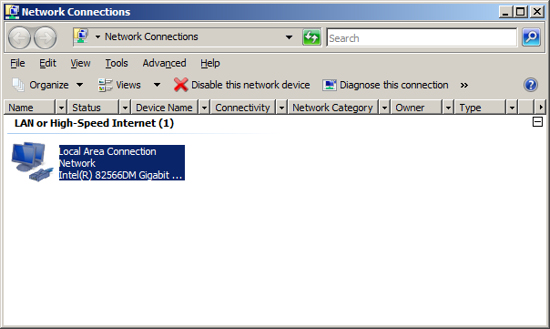
To change your IP address, click on "View Network Connections" in the Server Manager screen.
This will display the list of active network interfaces.
Double-click on your network adaptor to display the adaptors status.
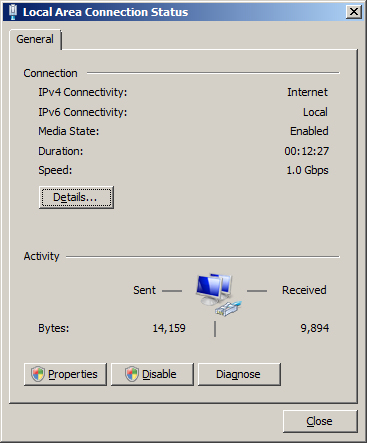
Press the Properties button.
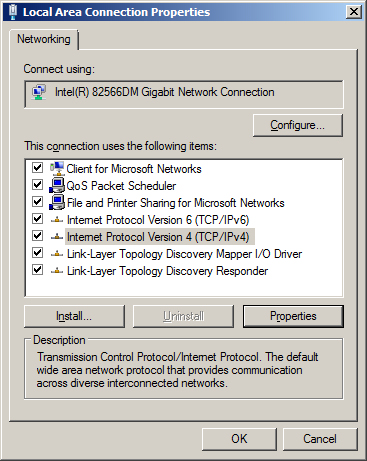
Highlight "Internet Protocol Version 4 (TCP/IPv4)" and press the Properties button.
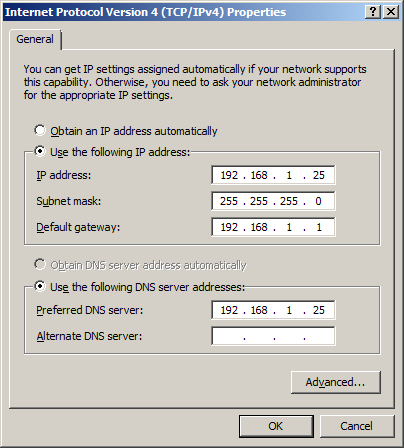
Change the radio button to "Use the following IP address" and enter an IP address you want to use for this server. In our example, we chose to assign this server the internal IP address "192.168.1.25". We also have a firewall appliance that operates as a gateway at the IP address "192.168.1.1".
NOTE: It is important to include this computer in the DNS list. You should list the IP address of this computer as the first entry in the list of DNS servers. In the "Alternate DNS server" field, enter the IP address of a DNS server provided by your ISP.
Press OK to save your changes.
Now you will need to modify the support for IP v6. If your network uses IP v6, then you will need to select "Internet Protocol Version 6 (TCP/IPv6)" and press the Properties button. Enter a static address. If you are not using IP v6, you can leave the IP v6 set to the default setting of DHCP.
NOTE: Exchange requires that IP V6 be enabled. Even if you do not use IP V6 you must leave it enabled. During the setup of Active Directory, the Active Directory Setup Wizard will check that both IP v4 and IP v6 have static addresses as long as the IP v4 address is static you can continue the installation. DO NOT DISABLE IP V6 or else the Exchange Hub Transport Service will not start.
At this point you should have all IP addresses on this server configured as static IP addresses. OR you have the IP v4 address configured as static and the IP v6 configured using DHCP. Press OK to save your changes and close the network connection screen.
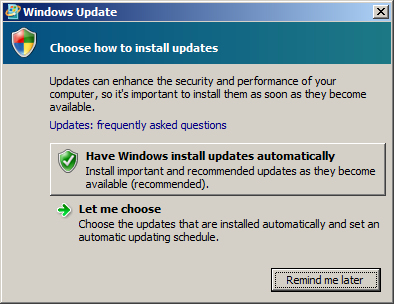
Activate Auto Update
The next step in making this server a domain controller is to activate auto update. Active Directory will not install until this computer has auto updates active. To activate auto updates click on the link "Configure Updates". Then select the option to have Windows automatically install updates. At this time Windows will download updates and will most likely need to reboot your computer. Allow the updates to be applied and the computer to be restarted until all updates are applied before installing Active Directory. You do not want to be in the middle of installing Active Directory when an auto update needs to reboot your computer.
Add role - Active Directory Services
The process of installing Active Directory consists of two steps, the first step is to install Active Directory and then you will need to configure your Active Directory. Once this is complete your Windows Server will now be a domain controller.
Step 1 - Install Active Directory
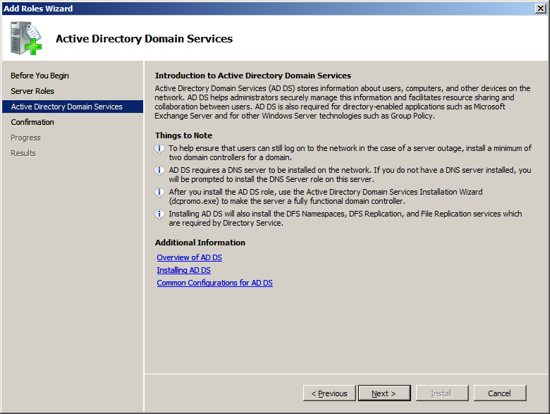
At the Computer Management Screen press the "Add Roles" link. At the Select Server Roles dialog check/tick the option "Active Directory Domain Services" and press Next.
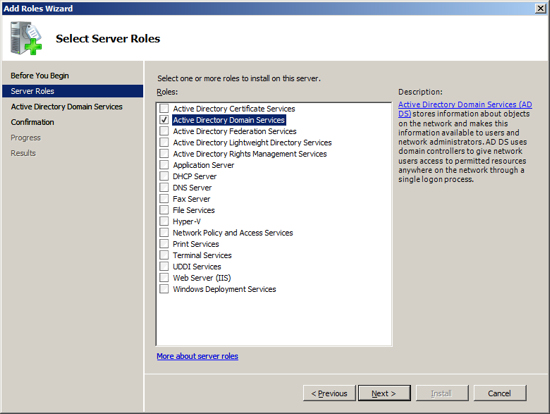
Active Directory Domain Services will present information about the changes it will make to your server. Review this information and press Next.
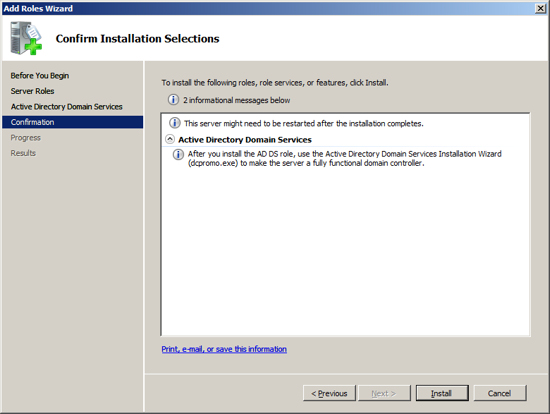
Now the installation will scan your configuration and inform you if there are any pre-requisites that you have not fulfilled. If the Active Directory Installation presents an errors, correct these at this time and then repeat the installation. Once the Setup program indicates that you have met all pre-requisite, then press the Install button to start the installation process.
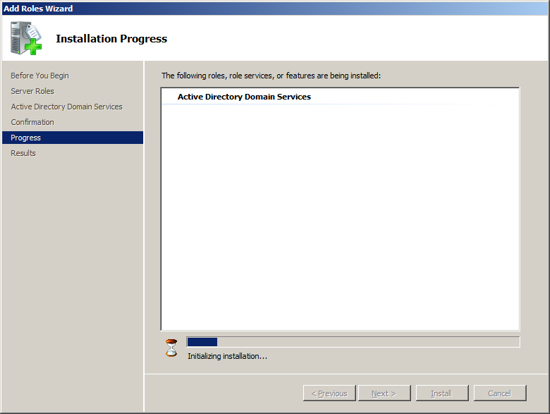
The setup program will now install Active Directory on your Server.
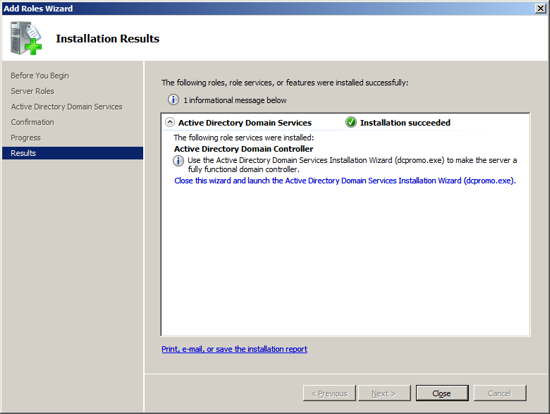
When the installation is complete you should see a message indicate "Installation Succeeded", press Close to return to the Server Management Screen.
Step 2 - Configure Active Directory
At the Server Management screen you should now see that you have 1 role installed. The Active Directory Domain Services may indicate that it is installed but there are errors. This is because the software is installed but not configured.
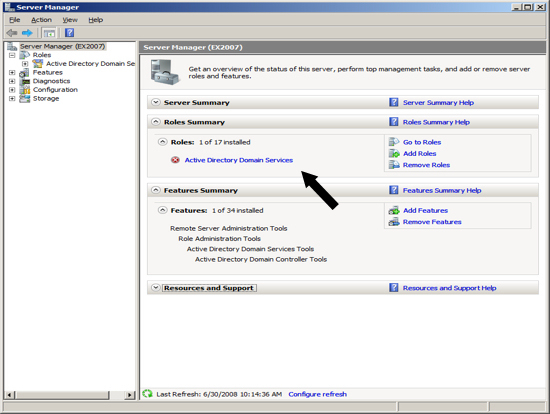
To configure Active Directory click on the line under Roles labeled "Active Directory Domain Services". The Server Manage will show you a page about the status of the Active Directory Role.
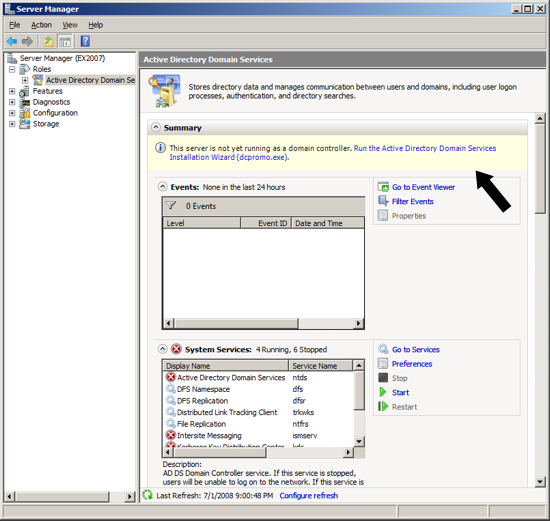
Click on the link "Run the Active Directory Services Installation Wizard (dcpromo.exe)" and the Active Directory Domain Services Installation Wizard will appear, press Next.
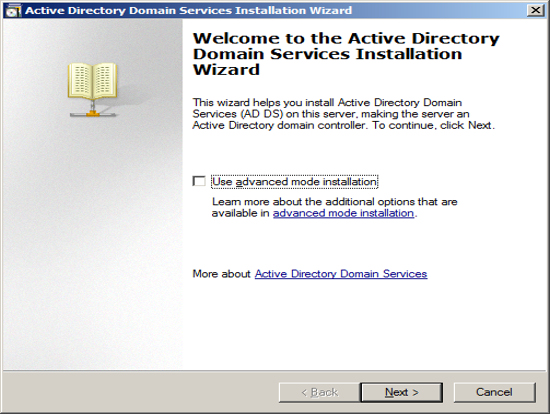
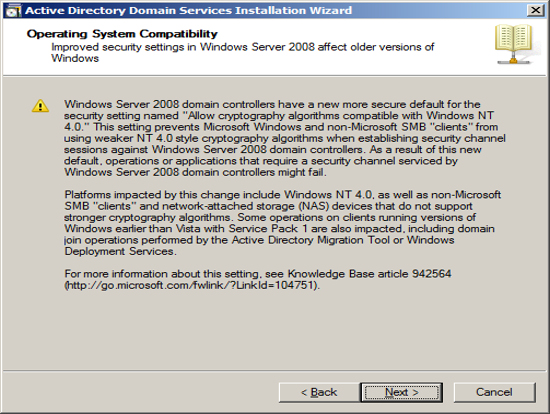
The Installation Wizard will present information about the version of Active directory, press Next.
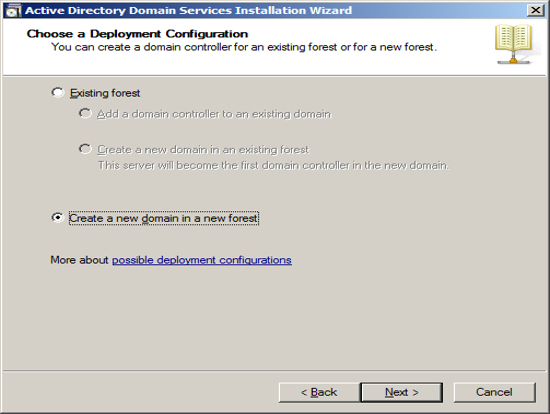
Since we are assuming this Exchange Server will be the first Domain Controller, we chose to create a new domain in a new forest. Press Next.
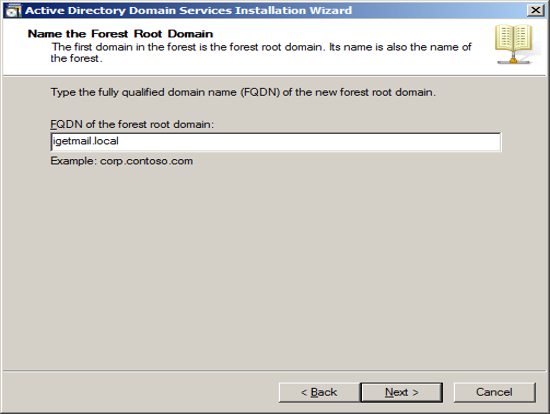
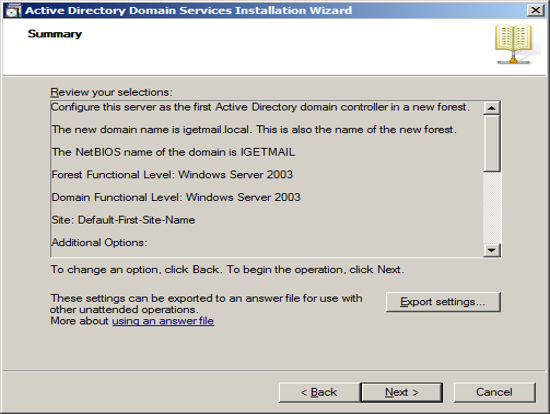
Enter the name of your domain. The domain name you enter here is the domain name that Exchange will associated with all of your email. If you use a hosting company to host your Internet Domain, then you may want to enter the name of your Internet domain with ".local". If you host your own Internet Domain then you would enter your domain name here.
In our example we are assuming that IGetMail.com is hosted at an Internet Hosting Company. Since we do not host IGetMail.com on this Exchange Server, we will use IGetMail.local to indicate our internal domain for IGetMail.
NOTE: Once you enter your domain name it is very hard to change it in the future, so you should take great care when enter this name.
Press Next once you have decided on the name of your internal domain, that will be your Active Directory Domain and the domain serviced by Exchange.
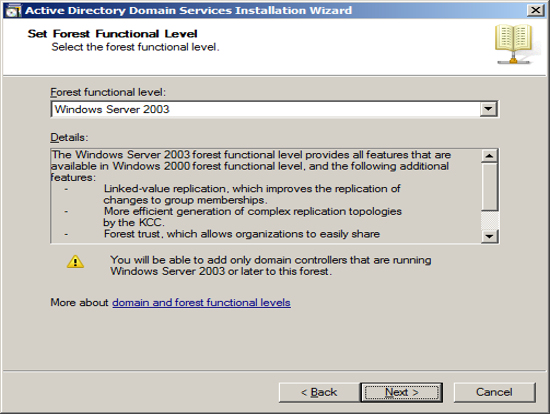
Next the Installation Wizard will ask you about compatibility. If you plan to have domain controllers running various versions of Active Directory then you will want to chose a function level to include the lowest version of Windows that you are using for domain controllers. Press Next.
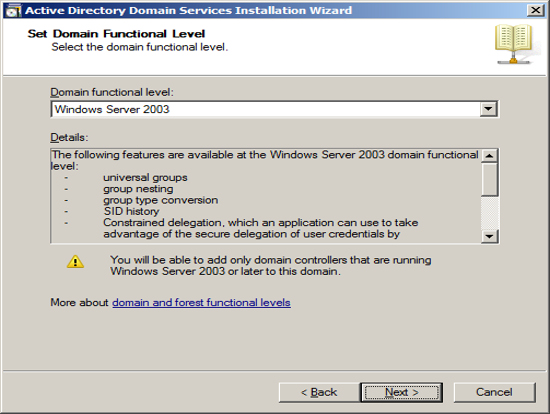
Next you will be asked a similar question which is at the domain level instead of the forest level on the previous screen. You should follow the same approach and include the function level to include the lowest version of Windows you plan to use for domain controllers. Press Next.
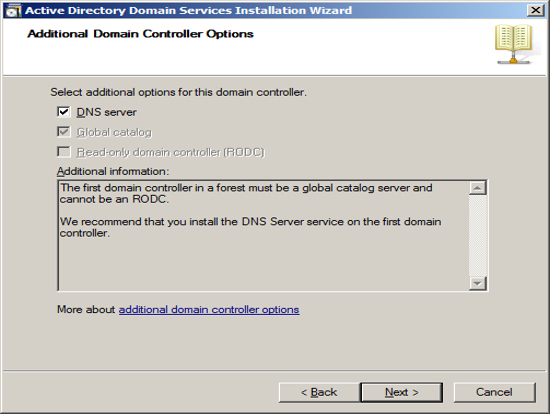
The first Domain Controller needs to have a DNS server running locally. The optimal location is to start out with having the installation wizard install the DNS server locally. Also it will automatically make this computer a global catalog server. Press Next.
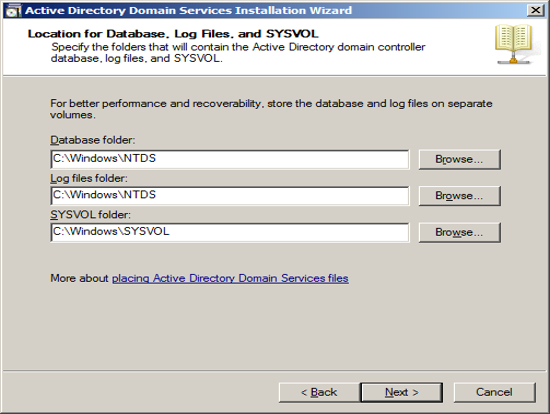
You can specify where you want Active Directory to store its data. If you only have on e drive in your Server then use the defaults. If you have multiple drives, you can select which drive to use. Press Next.
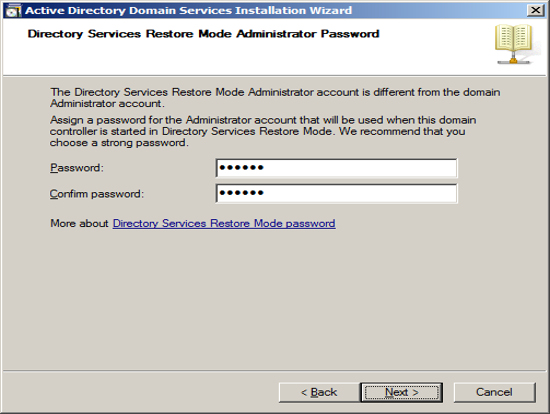
Should you need to restore Active Directory in the event of a hard drive failure you will need to boot your Server into a special mode called "Directory Restoration Mode". Should you need to boot your computer into this special mode, you will need to use a special password just for this restoration. You can define this password at this time. NOTE: This password is different than the administrator account and if you change the administrator password this password will not change. So you will need to store this password forever in a safe place. Press Next.
Now the Installation Wizard will summarize the configuration that it is about to create. Press Next to start the process of configuring your new Domain Controller.
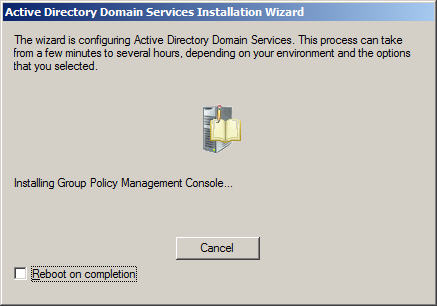
The Installation Wizard will show its progress as it configures your Server. This will take a long time.
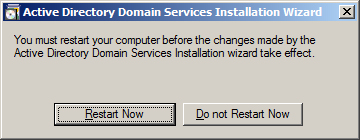
When the installation is complete, you will be shown a final screen. Press Finish.
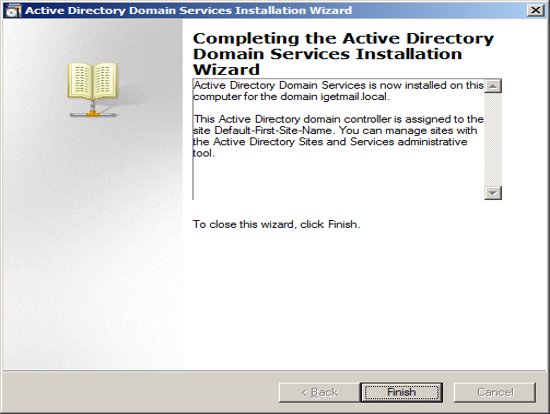
Then restart your computer.